
What happens when you take security leaders, engineers, and partners out of the usual hotel conference halls and bring them to the Austrian Alps? You get conversations that feel sharper, more personal, and more imaginative.
At Barracuda’s Tech Summit in Alpbach in 2025, cybersecurity was explained through football tactics and even the film Home Alone. But behind the analogies lie serious discussions about ransomware defense, tool sprawl, and the increasing burden of regulation.
Key Takeaways
Football strategies mirror cybersecurity, with attackers coordinating teams with defined roles.
Home Alone illustrates XDR: layered defenses, monitored entry points, and central visibility to stop intruders.
Akira ransomware cases proved that speed and correlation are vital in limiting damage from zero-day exploits.
Barracuda One reflects convergence, addressing tool sprawl with unified dashboards, alerts, and reporting.
AI is the “reckless intern” that accelerates detection and response but requires guardrails.
Regulation pressures MSPs to balance proportionate risks with compliance, shifting culture toward tougher accountability.
Football as a Blueprint for Defense
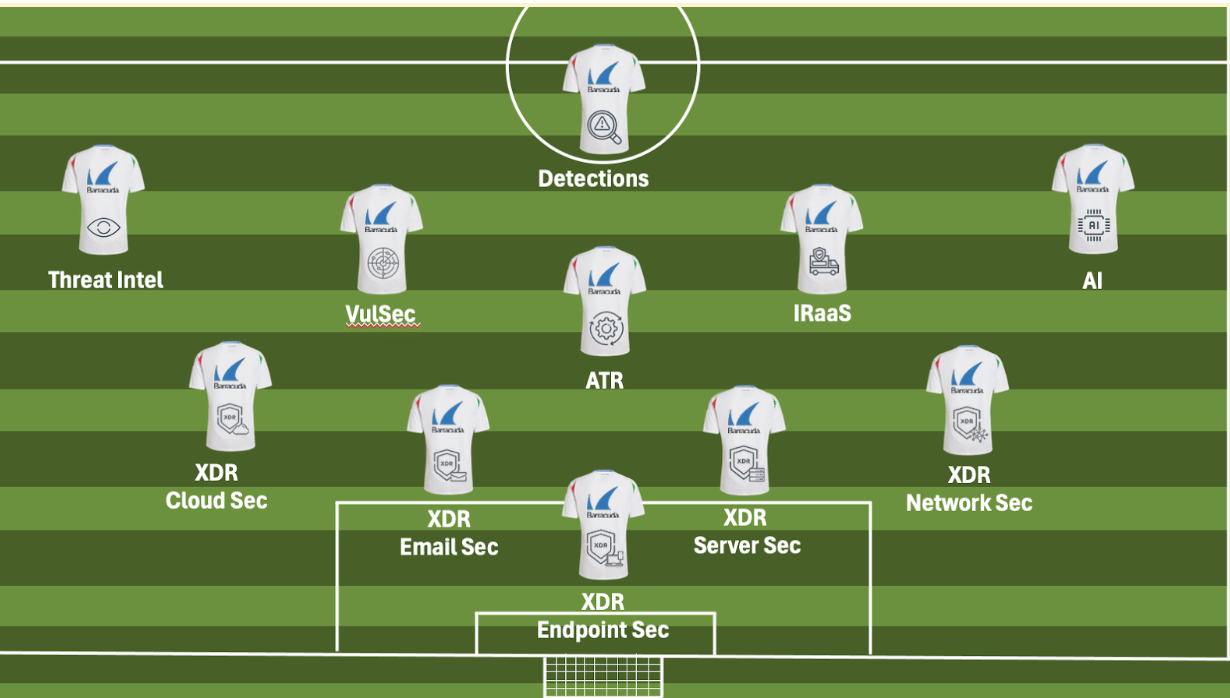
On stage in a mountain venue built into the rock itself, Adam Khan, VP of Global Security Operations at Barracuda XDR, used football to describe today’s threat landscape.
A slide of a formation appeared behind him, complete with attackers and defenders. The comparison was simple but powerful.

Attackers, he explained, are no longer amateurs or lone opportunists. They are organized like professional teams, each player with a defined role.
At the front are the strikers in the form of phishing campaigns and social engineering lures.
Behind them are midfielders who prepare the attack, such as malware droppers and credential harvesting schemes.
At the back are the players waiting for the decisive move, as well as command-and-control servers and ransomware payloads that execute once the defense has been compromised.
“Defense wins championships while offense sells tickets,” Khan reminded the audience. It is a saying commonly used in US sports, but it fits neatly into cybersecurity. Long-term success relies on a defense that is coordinated, resilient, and constantly adapting to new plays.
As in football, defenders cannot simply react to the ball; they must anticipate it. They must foresee runs, adapt their formation, and communicate constantly. For Khan, this mindset mirrors how security teams must respond to coordinated threats that are designed to exploit every weakness in the chain.
The Home Alone Analogy
Where football helped illustrate defense in broad terms, Khan also offered a story that anyone outside the industry could understand. He compared extended detection and response (XDR) to the Home Alone movie, where Kevin McCallister becomes the defender of his home against two burglars.
The synergies appear as he maps out the entry points, lays traps to slow down intruders, and crucially monitors their movements through windows and improvised cameras.
Khan described Kevin as the accidental chief information security officer (CISO):
“He identified the entry points, laid down protections, and most importantly, he watched on camera where the attackers were coming from. That visibility is XDR.”
The analogy resonated because it captured the three essentials of extended detection and response.
Understand the attack surface.
Create layered defenses around doors, windows, and other weak spots.
Maintain visibility across the whole environment to know where attackers are heading next.
Eric Russo, who leads Barracuda’s blue team of SOC analysts, reinforced the point. Visibility is what allows defenders to move from theory to practice. Without it, you are running blind. With it, you can correlate activity across endpoints, networks, and cloud environments, connecting seemingly minor events into a picture of a coordinated attack.
The power of both analogies lies in their accessibility. Cybersecurity can often be explained through acronyms and jargon. By grounding it in sport and film, Khan and Russo managed to bridge the gap between the technical community in the room and the business leaders who ultimately decide on investments.
Real Incidents & the Value of Speed
The football and film references were not just entertaining metaphors. They set the stage for describing real incidents. In recent months, Barracuda’s SOC team has tracked the Akira ransomware group as it exploited a vulnerability in SonicWall VPNs.
Customers who had not applied patches were vulnerable to intrusion. In several cases, the presence of XDR made the difference. Suspicious login attempts on firewalls triggered alerts that linked to activity on endpoints. Automated threat response tools, sometimes referred to as SOAR, then isolate machines showing signs of compromise.
The entire sequence, from attempted login to blocked process, played out in minutes. Without that correlation and speed, encryption could have spread through customer networks. Russo emphasised that ransomware defense today is about reducing time to respond. He said:
“If our analysts are Kevin McCallister, the best chance they have is when they can see the whole picture. The more visibility we have, the more likely we are of detecting threats before they become an issue.”
Convergence & the Barracuda One Vision
Where Khan and Russo described the fight on the ground, Barracuda’s Chief Product Officer Neal Bradbury spoke to the direction of travel. His keynote carried the message secured today, secured tomorrow. It was designed to reassure partners and customers that Barracuda is both defending against immediate threats and preparing for the future.
Bradbury’s central theme was convergence. Barracuda has expanded into a comprehensive portfolio encompassing email, application, network, and data protection. Many customers interact with a single product group without considering the broader context. The strategy now is to unify those solutions into a single platform known as Barracuda One.
The reason is tool sprawl.
A survey of more than 2,000 security professionals at the start of the year found that the excessive use of tools creates misconfigurations, slower responses, and unnecessary risk.
Bradbury argued that a platform approach does not mean abandoning specialist tools. It means centralizing alerts, configurations, and reporting so that organizations can make sense of them without being overwhelmed by noise.
“We want to be easy to buy, deploy, and use, and easy is hard,” he told attendees. The investment challenge is not just about building new features in isolation, but rather about making them work together seamlessly.
This focus reflects the shift towards managed services. Bradbury, who joined Barracuda with the acquisition of Intronis in 2015, has seen the change first-hand. Partners are no longer simply resellers. They are now providing proactive monitoring, managed detection, and even virtual CISO roles.
That change has influenced how Barracuda develops its products and how it supports service providers in delivering outcomes rather than just tools.
AI as the Reckless Intern
No modern security discussion can avoid artificial intelligence (AI). Bradbury described AI as “a reckless intern” that can be brilliant at speed but dangerous without oversight.
Within Barracuda, AI is being used in several ways:
The configuration of email security tools has been simplified through guided wizards. This reduces human error and speeds deployment.
Automated incident response allows managed service providers to remediate issues across dozens of tenants simultaneously.
In the SOC, AI models sift through millions of events to flag the combinations that matter.
For Bradbury, the value lies not in novelty but in reduced time to respond. A suspicious login, a malicious attachment, or an unusual process can all be investigated automatically.
Analysts are then freed to focus on proactive threat hunting and longer-term strategy. AI, in other words, is not a replacement for human expertise but an amplifier of it.
A Partner’s Perspective
Away from the keynotes, Richard Flanders of Aura Technology shared with me the view from the customer-facing front lines. His company, based in the UK’s south coast, supports hospitals, financial services, emergency responders, and other regulated sectors.
Flanders said:
“The common thread is regulation. ISO 27001, Cyber Essentials Plus, supply chain reporting. These requirements are increasing. We are duty-bound to help customers evidence compliance, and we must evidence to ourselves that we have chosen the right vendors.”
For him, Barracuda’s global presence and established contracts make it easier to provide that evidence. It shortens conversations with clients who need reassurance that suppliers are meeting the same standards they are asked to meet.
“No company can afford every security tool they need. It is about selecting the right tools for proportionate risks,” Flanders said.
That calculation is influenced by budgets, regulatory requirements, and the staff's ability to manage complexity.
Regulation is now forcing a tougher stance. Contracts, written recommendations, and more precise boundaries are becoming essential. Reputational damage can be as severe as financial loss when a breach occurs.
Regulation & Culture
The forthcoming UK Cyber Resilience Bill will add further pressure. It will make certification mandatory in more industries and sharpen directors' responsibilities. Fines and even prison sentences are on the table for negligence. Flanders believes this will finally drive investment in areas that boards have historically overlooked.
Training and culture are also shifting. Security awareness programs, phishing simulations, and disaster recovery exercises are becoming more common. Staff are increasingly seen as part of the defense rather than passive risks. Yet he stressed that this must move beyond annual compliance exercises. Real resilience requires continuous awareness and practice.
The message from Barracuda Tech Summit 25 was that defense must be strategic. Convergence is the path forward, and regulation is changing the stakes.
Football and Home Alone may seem like playful references, but they reflect more profound truths. Attackers are organized like teams. Defenders must coordinate like championship-winning squads. And just as Kevin McCallister needed visibility to protect his home, organizations need XDR to see threats across every entry point.=
The Bottom Line
AI will accelerate the challenge on both sides. Attackers are already experimenting with automation and reconnaissance at scale. Defenders must use the same tools to reduce response times and free experts to focus on proactive hunting.
The Alps provided the postcard backdrop, but the conversations were urgent. They centered on how to defend businesses today while preparing for tomorrow.
FAQs
How is AI changing cybersecurity according to Barracuda?
AI is seen as a “reckless intern” that speeds up detection and response but needs oversight to ensure accuracy and avoid costly mistakes.
How does convergence address cybersecurity challenges?
By unifying alerts, dashboards, and tools under Barracuda One, convergence reduces tool sprawl, improves response times, and makes security management more effective.
What role does speed play in defending against ransomware attacks?
Speed is critical in stopping ransomware before it spreads. With XDR and automated response, Barracuda’s SOC team can detect, isolate, and neutralize threats within minutes, minimizing damage and downtime.
