What happens when we finally admit that stopping every cyberattack was never realistic in the first place?
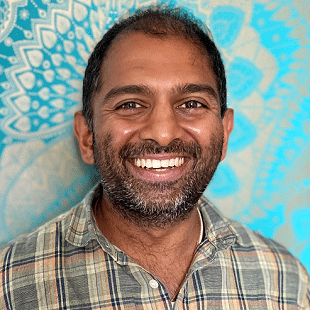
That is the thread running through this conversation, recorded at the start of the year when reflection tends to be more honest and the noise dial is turned down a little. I was joined by returning guest Raghu Nandakumara from Illumio, nearly three years after our last discussion, to pick up a question that has aged far too well. How do organizations talk about cybersecurity value when breaches keep happening anyway?
This episode is less about shiny tools and more about uncomfortable truths. We spend time unpacking why security teams still struggle to show value, why prevention-only thinking keeps setting leaders up for disappointment, and why the conversation is slowly shifting toward resilience and containment. Raghu is refreshingly direct on why reducing cyber risk, rather than chasing impossible guarantees, is the only metric that really holds up under boardroom scrutiny.
We also talk about the strange contradiction playing out across industries. Attackers are often using familiar paths like misconfigurations, excessive permissions, and missing patches, yet many organizations still fail to close those gaps. The issue, as Raghu explains, is rarely a lack of tools. It is usually fragmented coverage, outdated processes, and a talent pipeline that blocks capable people from entering the field, even as it claims there is a skills shortage.
One of the most practical parts of this conversation centers on mindset. Instead of asking whether an attacker got in, Raghu argues that leaders should be asking how far they were able to go once inside. That shift alone changes how success is measured, how teams prepare for incidents, and how pressure-filled P1 moments are handled when boards want answers every fifteen minutes.
We also touch on how legal action, public claims campaigns, and customer lawsuits are changing the stakes after a breach, forcing executives to rethink how they frame cyber investment. From there, Raghu shares how Illumio has been working with Microsoft to strengthen internal resilience at a massive scale, and why visibility and segmentation are becoming harder to ignore.
This is a conversation about realism, responsibility, and growing up in the industry. If cybersecurity is really about safety, not slogans, what would you want your organization to stop saying, and what would you prefer to hear instead?
Please feel free to upload the podcast. Here are also the links we discussed on the call:
Useful Links
Follow on Facebook, Twitter, LinkedIn, and YouTube
Thanks to our sponsors, Alcor, for supporting the show.
[00:00:04] What if the real measure of cybersecurity success was no longer about keeping attackers out, but about how little damage they can do once they're actually in? This is a question that feels uncomfortable for a lot of organisations, especially those who have spent years investing in preventative first strategies and promising the board that breaches simply won't happen. Yet as we kick off the new year, the headlines tell a very different story. Over the last
[00:00:34] 12 months, we've seen retailers, automotive brands and household names continuing to make the news for incidents that slip past those well-funded defences. And it is forcing a quiet rethink across the industry. And my guest today returns once again, he's a friend of the show from Illumio. And our conversation today is going to go right into the heart of that rethink, because he's been closely involved in the shift away from unrealistic prevention only mindsets
[00:01:04] towards a more cyber resilience mindset, where the goal is to contain disruption, protect critical systems and keep the business moving, even when it's under attack. And we'll talk about why attackers continue to succeed using familiar techniques like misconfigurations, missing patches, and also explore what containment really looks like beyond architecture diagrams and
[00:01:28] why success should be measured by how far an attacker can move rather than whether they can get in at all. And there's also going to be a powerful idea woven throughout this discussion, reframing cybersecurity as safety, not as an optional layer or a technical preference, but as a baseline expectation for running a modern business.
[00:01:51] So if you're a leader planning the priorities for the year ahead, we're going to ask the right questions about what being secure actually means today. Before I bring today's guest on, a quick thank you to my friends over at Denodo, who are passionate about logical data management for AI success. Because let's be honest, AI is evolving fast. But the elephant in the room is initiatives are still failing.
[00:02:16] Not because the models aren't good, but because the data foundation isn't ready. That's why organizations are increasingly turning to Denodo and logical data management. Denodo unifies your data across every cloud and every system without the need for massive replication. So if you're ready to make AI actually work, visit Denodo.com and put logical data management to work today. But enough scene setting for me.
[00:02:45] Let me introduce you to my guest. So a massive warm welcome back to the show. I struggle to believe this when I'm going to say this out loud, but nearly three years have passed since we last spoke. So can you tell everyone listening a little about who you are and what you do? It's a pleasure to be back. And I was actually, in fact, thinking back, I remember very clearly the first time I listened to one of your podcasts. It was actually on a drive down to, of all places, I think Chichester.
[00:03:15] So anyway, random fact. So I'm very well. And Anand Kamara here, VP of Industry Strategy at Illumio, the breach containment company. Since we last spoke, so many amazing things have been happening at Illumio. Of course, our market-leading segmentation product continues to go from strength to strength. But also in the last 12 months, we launched a new product, Illumio Insights.
[00:03:39] Detection response focused on identifying and addressing lateral movement risk in hybrid cloud environments. So that's been really exciting. We've had a bunch of really exciting announcements, not least some of those involving Microsoft in a not insignificant capacity, which have been incredible. And we're looking to even more momentum this year. So, yeah, absolutely. We're looking forward to 2026 after a fantastic 2025.
[00:04:10] Exciting times. There's so much that we need to catch up with today. I think I might need to have a new tagline for the podcast, though. Road trips accompanying people from Chichester to Chicago. Who knows? Sounds good. Sounds good. But we last spoke, as we said, three years ago. And a conversation then centered on proving the ROI of cybersecurity, a topic that's still relevant three years later.
[00:04:34] So looking at what we've seen recently and everything from retail and automotive, do you feel organizations have actually changed their behavior or just their language? Because we've seen that big Land Rover attack and the amount of money that cost. And MNS, for example, there's so many big, big attacks in the last 12 months. But what are you seeing here? Yeah, I think, first of all, in the UK, I feel that we've probably won the gold medal for high scale cyber attacks in 2025.
[00:05:01] I don't know if we wear that with pride or with sort of some form of embarrassment. I think the talk about whether we call it ROI or cybersecurity, whether we talk about the value generated, I think these are all the same words, right? Or synonymous with each other. And it's sadly, I think security has always had a problem about showcasing value or showcasing ROI, right?
[00:05:30] Because it's really difficult to measure and to say, oh, I had this and hence I stopped this cyber attack or I stopped the impact of this cyber attack. So the only real thing that we can quantify is risk reduction, right? We know that I had this risk because risk is something I can measure, right? My cyber risk is something I can measure.
[00:05:57] And when I put in place a control, I could then measure the cyber risk after the fact and say, okay, the cyber risk has either, hopefully it's gone down and gone down by a significant amount. And the control is effective or it's not. And the cyber risk hasn't gone down, which means that there's probably no value in that investment, right? However, ultimately, again, it's just a measure of the risk reduction.
[00:06:25] It is not a guarantee that a cyber attack will or will not be successful against your environment, right? And I think that's the challenge that we have in cyber is that what we would like to achieve is essentially reducing or taking the probability of a cyber attack being successful to zero. That is absolutely impossible, right?
[00:06:50] The only thing that we can realistically talk about is the reduction in cyber risk. We can measure it and we can reduce it. And that, I think, has got to be the shift that we take. And if we have a quick scroll down LinkedIn, we'll find many security leaders proudly saying they are proactive, they are preventative. But one of the things that stands out about what you've been talking about here is you've been quite blunt in calling this idea as quite unrealistic.
[00:07:17] So why do you think most security programs are still reactive rather than proactive in practice? Yeah. So, look, I'll always say prevention is ideal, right? So if we can prevent something, we should absolutely prevent it. However, the point about prevention being unrealistic is that we know that it is, and just going back to the last point,
[00:07:45] we know that it's absolutely impossible to prevent every single cyber attack, right? Because effectively what you're saying is, I know that there are a finite amount of bad things that could happen to me, and I have done everything that I can to ensure that those bad things cannot impact me. Well, what we know is that the number of possible bad things is not finite, right? So it is impossible to prevent everything.
[00:08:12] So the point about prevention being unrealistic is that it's really around prevention today has marginal gains. So in terms of, again, tying it back to reducing risk, right? Like prevention is not reducing risk to the extent that it was in the past, which is why everyone absolutely is now becomes very reactive, right? Because you try and be proactive.
[00:08:41] And when that fails, it's kind of, okay, let me wait till something happens, and then I'll respond and I'll react and respond to it, right? Which is, again, response is very important. But where I think we are seeing the shift, and we're absolutely seeing the shift, this is not just Illumio talking about this, but we're seeing this in the language that the regulators are using, in the language that organizations are using. It's all tied to the shift towards cyber resilience, right?
[00:09:11] The absolute importance of cyber resilience as the anchor of pretty much every cyber program now, and actually which is tied to the greater program of operational resilience, right? Organizations accept that cyber attacks or any kind of disruption, let's just not just say cyber, but any kind of unexpected or expected disruption is going to happen.
[00:09:37] And it is not feasible to just sort of sit there and say, well, I'll just accept the downtime. It's very much around, okay, let me plan for the unexpected. Let me try and maintain operations, maintain at least some minimum level of productivity, even in despite the sort of unexpected things, bad or innocuous. So given that that's really what's driving programs, and hence that comes into cyber resilience,
[00:10:06] then the shift is very much around, if we're talking about cyber resilience, is how do we withstand cyber attacks? Really, the thinking is then about how do I limit the impact of cyber attacks? How do I contain cyber attacks? And that is the shift in mentality. And this word that I spoke about, how every sort of regulation, et cetera, is anchored in cyber resilience,
[00:10:29] but also the term containment is something that is absolutely in each of these, right? Organizations, I'm paraphrasing, but organizations should be able to contain the impact of inevitable cyber attacks and ensure critical systems can be protected and can continue to operate. So we are very much in this era of containment. And containment can be proactive and reactive, right?
[00:10:58] Because that proactive piece is, I know the most important things to me. I know what some of my key risks are today. And here are the things that I can put in place to reduce those risks. But then the reactive piece is that, but I'm also prepared for the fact that the attacker is going to exploit something that I haven't yet got around to fixing or that I'm not even aware of.
[00:11:23] So how do I quickly respond to that and limit where the attacker can go and how far the attacker can go? So this is where we're seeing now organizations prioritizing. They may use different terms, but they're absolutely focused on resilience. And to focus on resilience, they have to prioritize containment. And as we've said, so many high profile incidents throughout the last 12 months.
[00:11:50] And I think it shows that attackers are succeeding through, if we're honest with each other, familiar paths. And we're talking about things like misconfigurations, missing patches and excessive permissions, etc. And if tactics have not evolved that much, where do you think organizations are still falling short? I don't want to oversimplify the problem, but what are you seeing here? But that's the thing, right, Neil, is that you joke and say you don't want to oversimplify it.
[00:12:16] But I'll say that actually the problem is quite simple. That is the frustration, right? Is that we, for so long, people hate it when, whether it's vendors or security professionals, talk about the fundamentals.
[00:12:35] But for so long, we have accepted some kind of implicit level of security or implicit level of protection or implicit level of trust that we haven't gone and addressed some fundamental gaps in our security capabilities. Which is why, then, to your point, well, why should attackers have to change their tactics?
[00:12:59] Why should attackers have to change their approaches if they can go and feast on the same opportunities that they've had thus far? At the very least, we should be forcing the attackers to do something different. Force them to work harder, right? And in all honesty, we're probably not forcing them to work significantly harder than they've had to before.
[00:13:25] And again, right, but also the available opportunities for the attackers are so vast. I'm talking like, yes, one organization may have a very mature security program, right, and have done a great job of addressing a lot of those fundamental risks. But hey, the organization next door is wide open.
[00:13:47] So the opportunity space for attackers is so vast because there are just so many organizations and so many environments where fundamental security gaps have just not been addressed. And I think you asked, is this a challenge with, is it about the tooling? Is it about the processes? Is it about the resourcing? I think it's a combination of the three, right? Right. Tooling, right, if you ask any organization and say, okay, well, how many security tools have you invested in?
[00:14:15] They will give you a laundry list of security tools, right? But if you then go and map those against the actual sort of controls, critical controls that they need to have, right, you will see that even though they've got that vast array of tools, there are still key gaps that they have in their coverage. So you're investing in lots and lots of tools. It's a good example. Just because you've got lots of tools, I mean, you can look at my tooling cabinet, right?
[00:14:42] I've got lots of different screwdrivers, but, right, they only all help me solve one particular problem, which is tighten or loosen screws. I need to go and paint a door. I don't have a brush, right? So it's not going to help. And that's the same way about sort of what we're talking about tool sprawl. What we're talking about is the fact that the coverage doesn't represent the investment, right? So there are gaps. So that's one.
[00:15:12] I think processes, to some extent, are outdated. And that's typically because there is always this constant tension between business agility, business acceleration, right, business transformation and security transformation, right?
[00:15:31] And while we sort of talk about the fact that security transformation, business transformation should always be in lockstep, right, and that way they're mutually beneficial, we know that security is always playing catch up, right? So there's always essentially a gap that you are chasing to address, right? So there's always this sort of the process piece never truly catches up.
[00:15:53] And on the resourcing side, there is a very tired debate about cybersecurity has a talent problem, right? Whatever it is, like there is 3 million shortfall or whatever in terms of headcount for cybersecurity jobs, right? But a personal experience of sort of a family friend, I was speaking to him when I was in India, and he's got like a master's in cybersecurity, right? Very like highly qualified.
[00:16:21] But if you look at the work experience, he's probably got six months of experience, right? So he's definitely fully qualified for some of these SOC analyst roles that he's looking for. However, he doesn't have the five years experience that they're demanding. So it's a chicken and egg problem. You've got a talent shortage. You've got people who are skilled who want the roles. But yet the way we are framing the experience for these essentially means that we can't possibly fill them, right?
[00:16:50] So we're not providing an easy path into cyber for people who are genuinely passionate and genuinely skilled in cyber, right? So this is a problem that we have to address. So these three things combined are essentially create a... We've essentially got that... We've created this situation where all of these problems are increasing, right? Yeah. I think it's such an important point you've raised there.
[00:17:20] It's not just about the lack of skills and the lack of people ready to enter the industry. It is easing that path in. And I also remember from our last conversation that one of the things that you said there was that the real question shouldn't be whether an attacker got into a system, but actually how far they were able to go once they were in. And I'm curious, for business leaders listening, what kind of shift in mindset is required here from their security teams and business leaders
[00:17:47] and uniting them to see that bigger picture and change that mindset? Because we've all heard, hey, but we've always done it this way. And there's nothing more damaging than hearing that phrase anywhere. But what kind of mindset is required here, do you think? Yeah, absolutely, right? And I think this, again, connects back to one of the earlier questions you asked is that if the sole aim of a security team is to stop an attacker getting in,
[00:18:13] then if the attacker or when the attacker gets in, does that mean they failed? Yeah. That, like, again, it's an unreasonable target. Whereas if you think about it, okay, cyber attacks are inevitable, right? We see that there's, like, a constant stream of cyber attacks. You just have to look at an external firewall, a perimeter firewall log to see the number of just continuous attempts, right,
[00:18:40] by folks to enter any organization, right? Because attackers are kind of constantly scanning and seeing, like, where there is an opportunity to get into an environment. So attacks are a constant and continuous. And even if an attacker finds a weakness, that weakness could be a misconfiguration, vulnerability, credentials, et cetera, phishing attack. Okay, they've established some kind of persistence of their target environment, right?
[00:19:09] They haven't yet been successful. What happens after the fact and your ability to limit what happens after that fact truly determines whether that cyber attack is successful and the sale of its success. So, yes, it would be great to prevent the attacker establishing that initial beachhead.
[00:19:33] But really what you want to ensure is that even if they do establish that beachhead, they can't go and, let's say, steal your sensitive data or take your critical systems offline. If you've been able to stop that or limit that significantly, then you have been successful in what you have done. That is a measure.
[00:19:55] Like, if you've been able to contain the impact of that attack, you've been able to reduce your attack surface, reduce your exposure to such an extent that the attacker, even if they get access to your environment, they've got very little place to go. So, that is a measure of success, right? So, it's very much around, I think the conversation is really around, okay, if the attacker gets into our environment, how far realistically could they go? How bad could this cyber attack get?
[00:20:25] That, if you're able to have a clear response to that question, right, that shows a security program that is maturing, that is heading in the right direction. I just want to give a big thank you to my sponsor, who is supporting every show, every episode across the Tech Talks network this month, because their backing helps me bring you conversations with leaders from every corner of the tech world, day after day.
[00:20:54] And this month, I'm proud to be partnering with Alcor. And anyone who's tried to scale an engineering team across borders, they will know firsthand how messy it can get. Because they deal with endless providers, then there's confusing rules to deal with in each and every region, and fees that always seem to surface at the last minute. Now, Alcor, they solve that by acting as a partner rather than just an intermediary.
[00:21:20] And they focus on tech teams that expand in Eastern Europe and Latin America, and they bring employer of record services together with recruiting. So, essentially, they help you pick the right country, source the right engineers, and assess them properly. And then get them active for you and your company within days. And one of the things that stands out for me is the financial transparency. Around 85% of what you pay goes directly to your engineers.
[00:21:49] Their fee goes down as your team grows. And if you ever wanted to bring your team in-house, you do so with no exit costs. That kind of clarity is why Silicon Valley startups, including several unicorns, have chosen Alcor. And you can find out more by simply going to alcor.com slash podcast or follow the link in the show notes below. And I think it was Mike Tyson said that everyone has a plan until they're hit in the face.
[00:22:16] And I think this is important to raise as well because we've all been in those P1 kind of environments where you're desperately trying to fix the problem, troubleshoot everything. And equally, at that same moment, the board is asking for updates every 15 minutes. And I think nearly every executive has admitted that they probably face obstacles when responding to incidents on top of that, often due to tooling, processes, or resourcing. So, in your view, what is the hardest to fix here and why?
[00:22:43] When you're transported into that P1 environment and so much is happening, because the game changes completely then, doesn't it? Yeah, I think the Mike Tyson quote is so relevant to cyber. And I think, firstly, the important thing is having a plan, right? So, if we flip the Tyson quote on its head and say, let's assume you're going to get punched in the face, what do you do next? Right? So, the important thing, the first thing is have a plan, right?
[00:23:13] Any plan is better than no plan. And that's the truth. The next thing is take time to test and validate your plan. Think of those kind of scenarios that could happen. The unexpected, like, I mean, I've done a ton of business continuity planning and DR testing, etc. But a lot of that, going back 10, 15 years, has been very much,
[00:23:41] okay, on this scheduled date and time, we are going to shut down a data center. Yeah, that's great. It's very important. It's valuable. But that's not how attacks happen, right? That's not how unexpected events happen. Unexpected means that you don't know when it's going to happen. So, are you prepared for that, right?
[00:24:02] Can you execute your plan even in that unexpected scenario versus when it's like a nicely planned DR test with a change control, right? Those are the things I think being able to plan and then having some form of incident response plan and having tested that and validated that, again, gives you an advantage over organizations that haven't taken that step, right?
[00:24:31] That would be at the most basic is have some form of response plan. What are you going to do? What are the first things you're going to go and look at? Identifying those critical systems, those things that are relevant to your organization. Actually, if we rewind and tie it back to the whole sort of cyber resilience narrative, right, is if we start from the premises that you're trying to maintain operational resilience, what are the systems, what are the processes, what are the business processes that are most relevant to your organization?
[00:25:00] And what are the applications and systems that those things are dependent on? And are those adequately protected and those adequately resilient? And then how in the space, during an incident, how would you ensure that they are maintained? This is all sort of high level, but that's kind of where your head should be going. Yeah, 100% with you. And containment is another word that comes up frequently in your thinking,
[00:25:26] especially when I've been keeping up to speed with some of the work that you're doing out there. And for the business leaders listening, what does effective containment look like inside a real enterprise environment? And by that, I mean beyond theory or architecture diagrams. What does it look like? Yeah, I think it's, again, right, let's tie containment to essentially reducing risk, right?
[00:25:50] And again, let's break it out into proactive and reactive containment. So proactive containment takes the shape of, where possible, reducing or removing unnecessary access and reducing the exposure of vulnerabilities and vulnerable systems. So at a very basic level, right? And that thing extends to identities, to segmentation, essentially.
[00:26:20] So reducing lateral movement risk. But then on the other side, so that's on the proactive side, right? And I think repeating what I said earlier, on the reactive side, it's having in place the process so that, again, tying it back to sort of incident response, that knowing what you are going to limit, what access you're going to, let's say, remove or restrict, should an incident start developing, right?
[00:26:49] So that essentially ties together proactive containment, which is essentially, let's say, pre-incident or pre-attack. So that's essentially how you improve the resilience of your environment proactively. And then reactive containment is saying, well, I know that even if I do all of these things, an attacker is still going to find some way. It may not be their ideal way, because I've done all of this work proactively,
[00:27:17] but they will find some other way to potentially have some level of success. But I know that I have solid response plans that allow me to quickly take action, because I can quickly identify and detect that active threat. And I can then put in place additional controls that will limit where the attacker can go, how far the attacker can go.
[00:27:43] So that the limit of that cyber attack, the impact of that cyber attack, is under my control versus under the control of the attacker. Now, I know you listen to podcasts when you're on road trips, but I was recently in a car with my wife. She had a commercial radio station on. And one of the things that I heard several times during this road trip was that UK radio stations are now having big ads on there,
[00:28:09] inviting customers to join the claim against Marks & Spencer's Co-op, Land Rover, and so many organizations that have suffered high-profile data breach. I don't know if you've heard that, but it completely changes the game. They're now inviting customers to join in attacking the businesses that suffered a breach. So from a board or C-suite perspective, how should leaders be rethinking cybersecurity investment if prevention alone is never enough to stop an attack?
[00:28:38] And then you've got all this other stuff going on if they are unlucky enough to suffer a breach. Yeah. I mean, firstly, those calls feel like ambulance chases, right? Classic sort of insurance claim ads and payment protection claim ads, right? The kind of ad that you should ideally just mute out when it's playing. So again, right? I think if you, again, think of this from the perspective of, or from a board level, right? What does a board understand?
[00:29:07] A board understands a very simple metric, right? And they track this across the organization. It's risk, right? Like how much risk am I happy to accept? And how much risk am I carrying, right? If I'm carrying more risk that I'm happy to accept, then I need to go and reduce that risk, reduce the risk that I'm carrying. And that absolutely translates to cyber, right? Quantify the cyber risk that you're currently carrying.
[00:29:37] And if it exceeds the risk that you're happy to accept, then you need to focus on reducing that risk, right? So then, okay. So now that we've established that, now let's talk about, well, where is your coverage? Where is the coverage and where are the meaningful gaps in your coverage? That if you don't address them, you are not going to effectively burn down that cyber risk.
[00:30:02] That gives you the pointer as to where you need to go and invest, right? And I was talking to a sort of a career CISO at an event just before Christmas. And they made a really interesting point, right? We talk about security. We talk about cyber security. But if you think about security, right? Security is, in many ways, security is an optional, right?
[00:30:31] You can choose to be less secure or more secure. Like you could have bodyguards sort of surround you as you walk down the street, right? Or you could just walk down the street without that. And one is more secure, potentially, and the other one is less secure. But we need to reframe key controls, not in terms of security, but in terms of safety. Because safety is not an option. If you framed it in that way, if I asked you, Neil, would you like to be safe?
[00:31:00] Would you like to be secure? You'll never say, I don't want to be safe. And that's the truth, right? That even though sort of how you frame key controls, right? And off is very much in the sense of this control is going to keep your environment safe, right? And until you address it, your environment is not safe. So you are compromising on your safety if you do not address this.
[00:31:28] That is the type of language that is going to create that light bulb moment saying, oh, yeah, I better go and fix that. Otherwise, this tape is going to play itself again and again and again. And as for yourselves at Illumio, obviously, it's three years since we last spoke. And you mentioned at the very beginning, you've been incredibly busy. You've collaborated with Microsoft to strengthen company cyber resilience and prevent breaches at scale. Tell me more about what you've been doing there and the big updates coming out of Illumio over the last six months. Yeah.
[00:31:58] So let's talk about Microsoft briefly, right? And this is all in the public domain. So Microsoft were the victim about two years ago, were the victim of a very sophisticated nation state cyber attack. And sort of on the back of that, what they realized was that they lacked the relevant visibility into their corporate IT environment
[00:32:26] and also the ability to effectively segment that environment at scale. When they were looking to address this, right? So if you think about, hey, this is not safe. We need to fix this. They said, well, the only game in town to really do this at the visibility and then the segmentation at the scale of Microsoft is Illumio's technology,
[00:32:49] which is why sort of they came to us and essentially we're helping them segment their internal IT environment. So that's kind of like just a small example of success. And that's at massive scale. But beyond that, we've sort of had like with Microsoft as a partner, we were a launch partner for their new Microsoft security store, integrating with their Sentinel.
[00:33:14] So you're probably aware that they sort of relaunched like Sentinel as sort of Microsoft Sentinel as their security ecosystem, as their security platform. So we're one of the launch partners for that. So our entire Illumio platform segmentation insights is all available via the security store and integrated directly into Microsoft Sentinel, right? So Microsoft Sentinel customers are able to benefit from all the capabilities of the containment platform directly from Sentinel
[00:33:42] and also for the integrated security co-pilot. So essentially conversational interface into Illumio data, into Illumio findings to help them address their lateral movement. So that's kind of like a brief thing about what we've been up to with Microsoft. Beyond that, what we've seen is that the whole market that we're in, right? The problem of lateral movement risk.
[00:34:08] Organizations, again, going back to say, this is a gap that we failed to address for many years and we need now to do something serious about it. We're definitely seeing a significant growth in that market, right? Because people are sort of sick and tired of looking at post-incident reports and saying, oh, well, you know what? One of the things this organization X didn't have was effective visibility and segmentation to their environment.
[00:34:31] So we're seeing a lot of organizations really like take that significantly more seriously and a real growth in the segmentation market, which is very exciting. I could go on, right? Well, I mean, we're recording this in early 2026. It's that magical time of year where we're all looking at doing things differently, maybe shifting that mindset, working differently and solving problems differently.
[00:34:56] So hopefully we've captured the imagination of people listening here and maybe inspired them to do something different. And hopefully we won't leave it three years until our next chat. But if we did, hypothetically, fast forward another three years, and I appreciate in the modern world, three years is like 10 years in old money. But what would you hope that organizations stop saying about cybersecurity? And what would you like to hear instead when they talk about things like preparedness and resilience?
[00:35:25] You just want one thing or do you want 100? Go for it. The floor is yours. So I think a key thing that I would like to see, right, is that so one thing that we haven't even touched on is zero trust. And there has been a lot of zero trust has had a lot of, let's say, negative press, right? It sort of had its it sort of had the hype. It's gone through that all states of the hype cycle.
[00:35:53] But I do think that there is a realization, whether you want to call it zero trust or you want to call it something else, that essentially removing implicit trust, implicit access in any environment is of paramount importance.
[00:36:08] So what I would hope is that over the next three years, the adoption of zero trust, the adoption of sort of principles of least privilege across all sort of control areas just becomes different. So that there's no debate about whether zero trust is the right strategy or not, because it's just implied in essentially our approach to cyber, right?
[00:36:37] In that we don't have to talk about it anymore. And it's just what most organizations are doing. Because if we see that change, then what we will see is that as a result of that, the effect will be that organizations are better prepared to contain the impact of cyber attacks. As a result, they have reduced their cyber risk. As a result, they are more cyber resilient. They're more resilient, right?
[00:37:07] So we're going to see those sort of like those knock on, knock on effects. However, as I've said before, right, if we continue to sort of be like those three monkeys, closing our eyes, closing our ears, closing our mouths, right? And then just hoping that just by doing a lot of talking, things will improve. It doesn't take a genius to say that actually things will get much worse. And I think that's a powerful moment to end on.
[00:37:34] And for anyone listening, want to connect with you or your team or just learn more about some of the big announcements coming out of Illumio this year and beyond. Where would you like to point everyone listening? I mean, Illumio.com is the place to go. We're obviously very active also on LinkedIn. We've got a growing following on Instagram as well. So if you want a bit more fun and informal corporate content, go and head over to our Instagram channel. I think they're all, all the handles are at Illumio. Check out our podcast, Neil.
[00:38:03] So just plug our podcast, the segment. It's a multi-award winning podcast. So go check that out. Almost as illustrious as yours, though not quite. So yeah, we've had some great guests and I think season four is about to start soon. So that's also, and yeah, just more content for people who want to listen to it. Awesome. What's the name of the podcast? I'll include a link to that. The segment. The segment. Okay.
[00:38:29] I'll add a link to that for people to check out and as well as the links and everything else. And I love people listening. Feedback. What are you taking away from this interview today? And anything that resonated with you? Please share with myself and my guests. And more than anything, I just thank you for coming back on here and shining a light on this and really appreciate your time as always. And we won't leave it three years until we speak again, but thanks so much. It's always a pleasure, Neil. Thank you so much.
[00:38:56] So if breaches are inevitable, what does being prepared look like? This is a thought that stayed with me after speaking with my guests today. This idea that containment rather than prevention, that is becoming a true benchmark of cyber maturity, especially as it challenges a lot of those long held assumptions, because it asks leaders to accept
[00:39:18] uncertainty, but also take far more responsibility for how systems are designed, segmented and operated day-to-day.
[00:39:57] So a sobering reminder here. Attackers are rarely doing anything particularly clever. They're simply exploiting gaps that organisations already know about, but have not yet addressed. So in that sense, resilience is as much about a discipline and focus as it is about innovation. So I'll have links in the show notes so you can explore everything we talked about, including the latest announcements from Illumio in more detail. And I'd generally love to hear your perspective.
[00:40:26] Does shifting the focus from prevention to containment, does that feel like progress to you? Or does it feel like lowering the bar? Or is it just more realistic? As we move into a world where disruption is part of doing business, how confident are you that your organisation could limit the impact when, not if, something goes wrong and that P1 hits? As always, techtalksnetwork.com, LinkedIn X, Instagram just at Neil C. Hughes, techtalksnetwork.com.
[00:40:56] Let me know your thoughts. I'll be back again tomorrow. But it's time for me to check it out now. Speak with you all tomorrow. Bye for now. Bye for now.

