
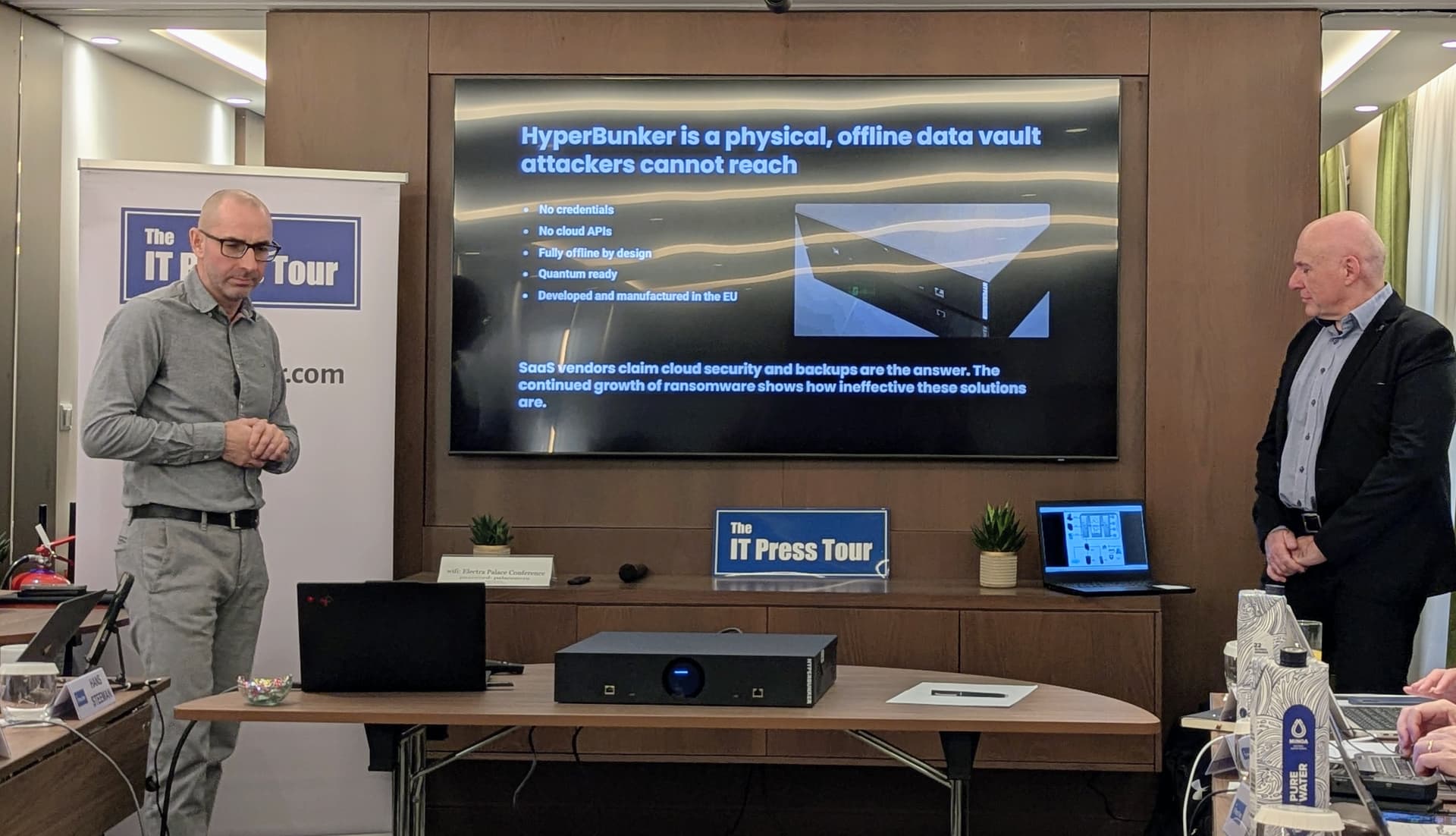
At the 65th IT Press Tour in Athens, Imran Nino Eškić and Bostjan Kirm from HyperBunker spoke candidly about a problem that many organisations only discover too late: their backups are not as secure as they think. Sure, they had backups, but attackers reached them first.
HyperBunker exists because, across tens of thousands of real-world recovery cases, the same failure kept repeating. Credentials were stolen. Although backup repositories were encrypted, cloud replicas were compromised long before anyone realised an incident was underway. When the moment to recover arrived, there was nothing left to trust.
HyperBunker was not created by a cybersecurity team chasing the latest threat model. It was built by people who spent decades in data recovery labs, dealing with the aftermath of breaches, hardware failures, insider sabotage, and ransomware attacks that had already run their course.
HyperBunker is a European-built offline vault that keeps one clean, immutable copy of an organisation’s most critical data completely out of reach from ransomware, insider threats, and even future quantum-enabled attacks.
The founding team brings more than 25 years of recovery experience and has worked on over 50,000 real data-loss cases. Their perspective is shaped less by prevention claims and more by forensic reality. In their words, the worst moment is not discovering you have been attacked. It's learning that recovery is impossible.
That experience led them to a hard conclusion. In modern environments, almost nothing is truly offline anymore, and attackers know it.
Why Modern Backups Keep Failing
Most backup strategies assume that immutability, air gaps, or cloud isolation will hold under pressure. HyperBunker’s team argues that these assumptions no longer match reality.
The Picus Blue Report 2024 paints a stark picture. Only a small fraction of attacks trigger alerts. A large share of environments expose paths to full administrative control. And ransomware prevention rates remain inconsistent, depending on the group behind the attack. Meanwhile, AI is accelerating intrusion techniques faster than human response cycles can keep up.
In practice, this means detection is often late, containment is incomplete, and online backups become collateral damage. By the time an organisation realises it needs its backups, attackers have already reached them.
What HyperBunker Actually Is
HyperBunker is designed to ensure that, even in the worst-case scenario, organisations will have a clean, uncorrupted copy of their most vital data available for recovery. It does not replace existing backup software, cloud storage, or security tools, but serves as an offline vault that ensures this critical data remains available when all other options may have failed.
This unique function, providing a survivable, always-recoverable copy of essential data, is what HyperBunker calls the survivability layer. It is the layer relied upon when all others cannot be trusted.
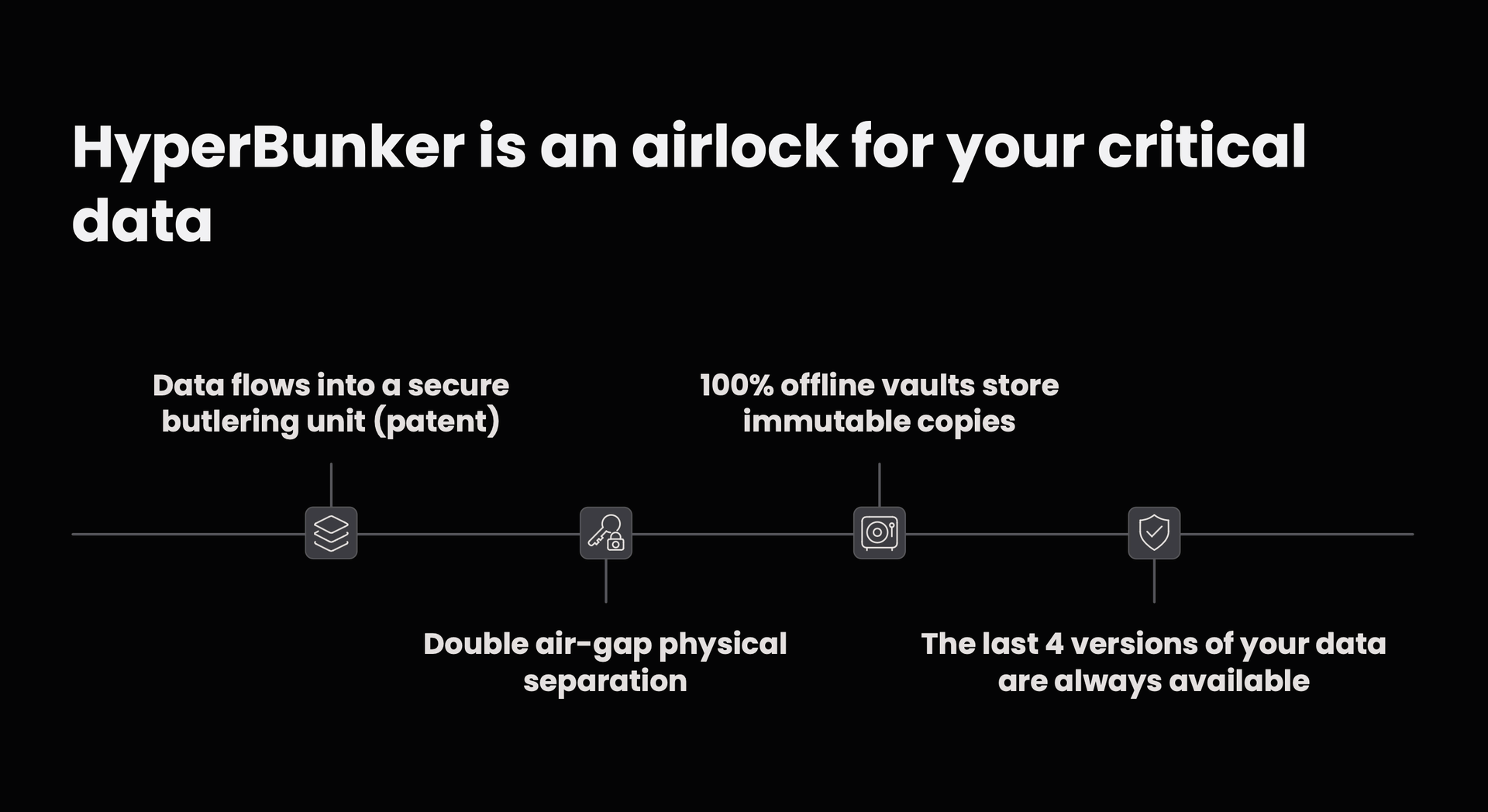
At a physical level, HyperBunker is a hardware-based offline data vault. It uses a patented “butlering” mechanism that behaves more like an airlock than a network device. Data can move in only one direction, passing through two physical air gaps that are never open simultaneously. Once data reaches the cold vault, it is fully offline.
There are no credentials to steal, no cloud APIs to abuse, and no remote access paths to exploit. Even the monitoring channel is one-way only. If attackers cannot see it, they cannot hit it.
Immutability Without Connectivity
A key design choice is that HyperBunker does not validate incoming data for cleanliness at the point of ingestion. Instead, it ensures that once data is stored, it cannot be executed, encrypted, or altered by anything online.
Multiple immutable versions are retained, allowing organisations to roll back to earlier states if needed. Restoration requires physical presence at the device, reinforcing the separation between online compromise and offline recovery.
This approach reflects the team’s recovery-first mindset. They are less concerned with perfect prevention and more focused on guaranteeing that at least one trustworthy copy survives.
HyperBunker is seeing early adoption in sectors where downtime is existential rather than inconvenient. Energy and utilities, healthcare, manufacturing, transport, finance, and government all face regulatory, safety, or continuity obligations that make recovery certainty non-negotiable.
Cyber insurers are paying attention for the same reason. Insurance losses are often driven not by the initial breach but by failed recovery efforts. That is why U.S.-based cyber insurer Cowbell added HyperBunker to its marketplace after validating its offline approach.
Incident responders report a similar pattern. In post-mortems, the only data that reliably survived was that which attackers could not reach.

A Different Way to Think About Resilience
The HyperBunker team is careful to say they are not anti-cloud or anti-backup software. Cloud platforms and modern backup tools do what they are designed to do: store and move data efficiently. The problem arises when organisations assume that connected systems can serve as a last resort for recovery.
HyperBunker is deliberately designed to sit behind all other layers as the final fallback when every other layer has failed. One of the things that stood out to me most in Athens was how calmly the team talked about worst-case scenarios. They are not selling fear. They are selling certainty.
HyperBunker reflects a growing recognition that resilience is becoming a governance issue, not just an IT checkbox. As ransomware, regulation, and geopolitical risk converge, offline recovery is increasingly looking like an edge case rather than a baseline requirement.
Having already secured €800,000 in seed funding to ramp up production of its new anti-ransomware black box, I will be following HyperBunker closely as they scale. If you were to hear them on a future podcast episode, which questions or concerns would you like addressed?
Let me know what you would challenge, clarify, or explore so I can bring these topics forward in a follow-up conversation on my podcast.
